The DK7, a modern piece of hardware, has emerged as a digital heir to the legendary Enigma Machine. While the Enigma was mostly used for encryption during World War II, the DK7 takes its principles and applies them to current challenges in the realm of cybersecurity.
This complex device employs a set of mathematical formulas that are continuously evolving to stay ahead of potential threats. Utilizing the power of quantum technology, the DK7 promises unprecedented levels of protection for sensitive data.
The DK7's functions extend beyond conventional encryption. It can also be used for authentication, key generation, and other cryptographic processes. With its adaptability, the DK7 has the potential get more info to revolutionize the way we defend our digital world.
Exploring the Future of Cybersecurity
The landscape of cybersecurity is in constant flux, with threats evolving at an alarming rate. To stay ahead of the curve, organizations must embrace innovative strategies. DK7, a leading-edge platform, prompts this evolution by providing advanced tools and resources to combat emerging attacks. DK7's user-friendly interface empowers security analysts to analyze threats in real-time, enabling them to respond risks proactively. By utilizing artificial intelligence and machine learning, DK7 identifies hidden patterns and anomalies, providing valuable insights to improve security posture. In the face of ever-evolving threats, DK7 stands as a vital asset for organizations seeking to strengthen their cybersecurity defenses.
DK7: A Quantum Leap in Encryption Technology
The cybersecurity landscape is shifting at an unprecedented pace. Traditional encryption methods, while effective for their time, are susceptible to sophisticated attacks. Enter DK7, a groundbreaking quantum-resistant encryption protocol that promises a paradigm shift in secure communication. DK7 leverages the principles of quantum mechanics to create impossibly secure cryptographic keys, rendering them protected from even the most powerful classic computing algorithms.
- Additionally, DK7's innovative design ensures fast and efficient data transmission, reducing latency without compromising security.
- Such a revolutionary technology will revolutionize diverse sectors, from financial institutions to individual users, protecting sensitive information in an increasingly connected world.
The DK7 Protocol : Unlocking the Secrets of Secure Communication
In the realm across modern communication, security stands as a paramount concern. Data breaches and unauthorized disclosure threaten to erode trust and compromise sensitive information. To address these challenges, innovative solutions are constantly emerging. One such solution is DK7, a groundbreaking protocol designed to ensure secure and robust communication.
- The DK7 Protocol's innovative architecture leverages advanced cryptographic techniques to secure data in transit and at rest.
- This protocol is designed to be versatile, integrating a diverse selection of communication channels.
- Additionally, DK7 implements strict identity verification measures to deter unauthorized access.
By employing these sophisticated security features, DK7 facilitates users to perform confidential communication with assurance.
Data Integrity with DK7
The digital age presents both unprecedented opportunities and challenges. With personal data increasingly vulnerable to cyber threats, robust data protection solutions are paramount. Enter DK7, a cutting-edge platform designed to protect your valuable assets in the ever-evolving digital landscape.
DK7's advanced algorithms and multi-layered security protocols provide a reliable framework for cybersecurity. By implementing DK7, organizations can minimize the risk of data breaches, ensuring the confidentiality of their clients' information.
- Furthermore, DK7 offers a user-friendly interface, making it accessible to businesses of all sizes.
- Leveraging commitment to continuous improvement, DK7 remains at the forefront of digital defense technology.
In conclusion, DK7 presents a compelling solution for organizations seeking to enhance their data protection posture in the digital age. Its versatility and security make it an invaluable asset for any entity handling sensitive information.
Code-Breaking Revolution
DK7 is pushing the boundaries of code-breaking, offering unprecedented measures of security and robustness. This next stage of cryptographic technology utilizes cutting-edge algorithms to protect sensitive data from even the most resourceful attackers. With its scalable design, DK7 can be integrated to meet the specific needs of various sectors. As threats become increasingly sophisticated, DK7 stands as a crucial tool in the ongoing battle to protect our digital world.
- In addition
 Alfonso Ribeiro Then & Now!
Alfonso Ribeiro Then & Now!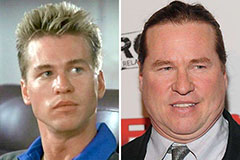 Val Kilmer Then & Now!
Val Kilmer Then & Now!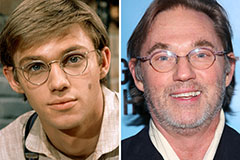 Richard Thomas Then & Now!
Richard Thomas Then & Now! Meadow Walker Then & Now!
Meadow Walker Then & Now!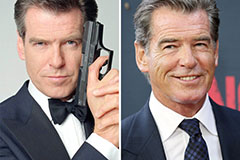 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!